About Armitage
Armitage is a scriptable red team collaboration tool for Metasploit that visualizes targets, recommends exploits and exposes the advanced post-exploitation features in the framework. Through one Metasploit instance, your team will:
- Use the same sessions
- Share hosts, captured data, and downloaded files
- Communicate through a shared event log
- Run bots to automate red team tasks
Armitage is open source software developed by Raphael Mudge's company Strategic Cyber LLC. However, Cobalt Strike is the commercially supported big brother of Armitage.
Armitage organizes Metasploit's capabilities around the hacking process. There are features for discovery, access, post-exploitation, and maneuver. This section describes these features at a high-level, the rest of this manual covers these capabilities in detail.
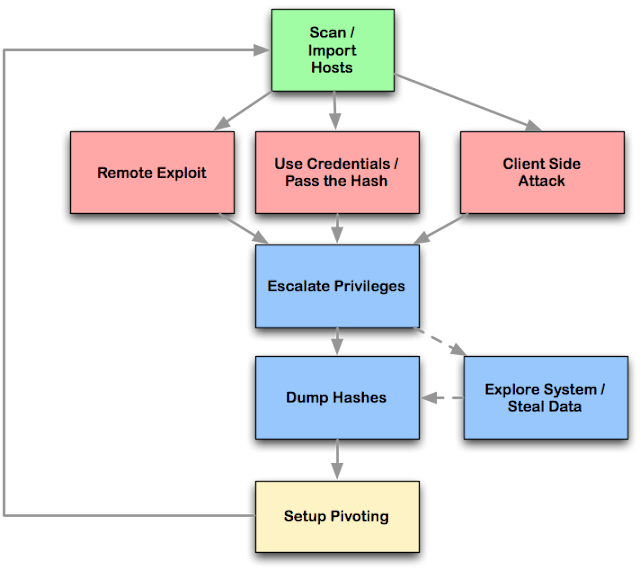 Armitage's dynamic workspaces let you define and switch between target criteria quickly. Use this to segment thousands of hosts into target sets. Armitage also launches scans and imports data from many security scanners. Armitage visualizes your current targets so you'll know the hosts you're working with and where you have sessions.
Armitage's dynamic workspaces let you define and switch between target criteria quickly. Use this to segment thousands of hosts into target sets. Armitage also launches scans and imports data from many security scanners. Armitage visualizes your current targets so you'll know the hosts you're working with and where you have sessions.
Armitage recommends exploits and will optionally run active checks to tell you which exploits will work. If these options fail, use the Hail Mary attack to unleash Armitage's smart automatic exploitation against your targets.
Once you're in, Armitage exposes post-exploitation tools built into the Meterpreter agent. With the click of a menu you will escalate your privileges, log keystrokes, dump password hashes, browse the file system, and use command shells.
Armitage makes it trivial to setup and use pivots. You'll use compromised hosts as a hop to attack your target's network from the inside. Armitage uses Metasploit's SOCKS proxy module to let you use external tools through your pivots. These features allow you to maneuver through the network.
The rest of this manual is organized around this process, providing what you need to know in the order you'll need it.
Package dependency before you install Armitage
Armitage exists as a client and a server that allow red team collaboration to happen. The Armitage client package is made available for Windows, MacOS X, and Linux. Armitage does NOT require a local copy of the Metasploit Framework to connect to a team server.
These getting started instructions are written assuming that you would like to connect to a local instance of the Metasploit Framework.
Armitage requires the following:
- Metasploit Framework and its dependencies.
- PostgreSQL Database
- Nmap
- Oracle's Java 1.7
To quickly install all of the dependencies, you have a few options:
- Use a Linux distribution for penetration testing such as Kali Linux.
- These distributions ship with Metasploit and its dependencies installed for you.
- Use the MSF Installer Script created by DarkOperator (This option will setup an environment that uses Git for updates).
- Use the official installer provided by Rapid7 (This option will require you to register with Rapid7 to get updates).
Setup Instructions to install Armitage in Kali Linux
- Open a terminal
- Initialize the database: service metasploit start
- Stop the metasploit service: service metasploit stop
- Extract armitage: tar zxvf armitageDDMMYY.tgz, where DDMMYY is version or date when armitage has launched.
How to Start Armitage
- Open root terminal
- type apt-get install armitage
Before you start Armitage, make sure the postgresql database is running:
- type service postgresql start
If you get a missing database.yml error, type:
- type service metasploit start

If you are searching for information regarding how to get credit cards on the dark web you should keep in mind that all links on the Internet are not safe and should be carefully looked at before making a decision on applying for one or purchasing one from an online merchant outlet Read more about my website: dark web links
ReplyDeleteFULLZ AVAILABLE WITH HIGH CREDIT SCORES 700+
ReplyDelete(spammed FROM Credit Bureau of USA)
=>Contact 24/7<=
Telegram> @leadsupplier
ICQ> 752822040
Email> exploit.tools4u@gmail.com
FRESHLY SPAMMED
VALID INFO WITH VALID DL EXPIRIES
*All info included*
NAME+SSN+DOB+DL+DL-STATE+ADDRESS
Employee & Bank details included
CC & CVV'S ONLY USA $8 FOR EACH
$1 for SSN+DOB
$2 for SSN+DOB+DL
$5 for High credit fullz 700+
(bulk order negotiable)
*Payment in all crypto currencies will be accepted
->You can buy few for testing
->Invalid or wrong info will be replaced
->Serious buyers needed for long term
->Very fast delivery
PLEASE DON'T ASK ANYTHING FOR FREE
TOOLS & TUTORIALS AVAILABLE FOR SPAMMING & HACKING
(Carding, spamming, hacking, scam page, Cash outs, dumps cash outs)
SQL Injector = 250$
Premium Accounts (Netflix, coinbase, FedEx, Pornhub, etc) =25$
Paypal Logins = 150$ (10 Logins)
Bitcoin Cracker = 500$
SMTP Linux Root = 300$
DUMPS with pins track 1 and 2 = 85$
Socks, rdp's, vpn = 25$
Php mailer = 25$
Server I.P's = 100$ (1k ip's)
HQ Emails with passwords = 100$ (1k emails+pass)
*If you need a valid vendor it's very prime chance, you'll never be disappointed*
Telegram> @leadsupplier
ICQ> 752822040
Email> exploit.tools4u@gmail.com